LetsDefend: Bash Script Challenge
Walkthrough of a suspicious YARN script: tracing environment variables and log paths, then following a chained download, a base64-decoded payload, and the remote staging IP.
Read article →6 writeups
Walkthrough of a suspicious YARN script: tracing environment variables and log paths, then following a chained download, a base64-decoded payload, and the remote staging IP.
Read article →
Email header and attachment analysis of a phishing email. Analyzed email headers and malicious attachments. Associated technique to its respective MITRE ATT&CK technique.
Read article →
Breakdown of UW-Stout's CTF challenges and key takeaways that came from such challenges.
Read article →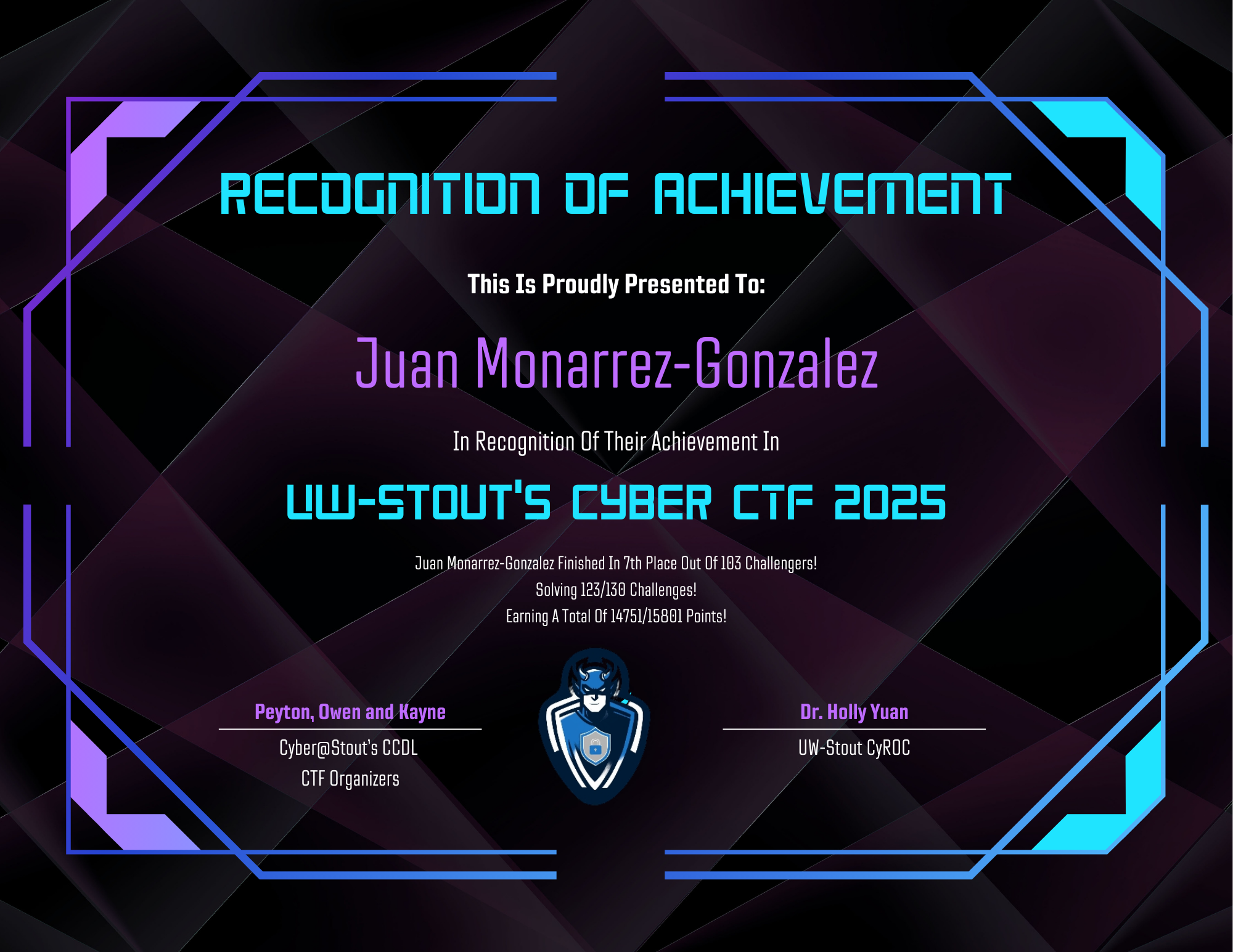
Analyzed an MD5 hash of a malicious file using sandbox reports. Extracted vital information and mapped identified behaviors to MITRE ATT&CK techniques.
Read article →
Easy rated Linux box showcasing basic enumeration tactics, web application exploitation, and identifying file misconfigurations to escalate user privileges
Read article →
Easy rated Linux machine. Covers VPN setup, nmap, and Telnet. Root access via default blank password on Telnet. Basic linux commands to view flag.txt file.
Read article →